
Contact us
Our team would love to hear from you.
Re-engineered Blockchain technology with improved speed, scalability and security allowed creating a truly decentralized and widely accessible cryptocurrency payment system.

Our customer is Dragon Infosec, Ltd., a cybersecurity and cryptography group that specializes in advanced protection solutions against cyberattacks, forensic analysis and tracing, Blockchain networks, AI, and cryptocurrencies. Having vast experience in the security industry and expertise in AI (deep learning and neural networks), the company wanted to create a new cryptocurrency. EffectiveSoft was chosen to re-engineer the existing Blockchain technology with the aim to decentralize it, increase its speed, improve security and minimize resource usage.
Temtum
UK
Blockchain
Mobile crypto wallet
JavaScript (EcmaScript 6), TypeScript
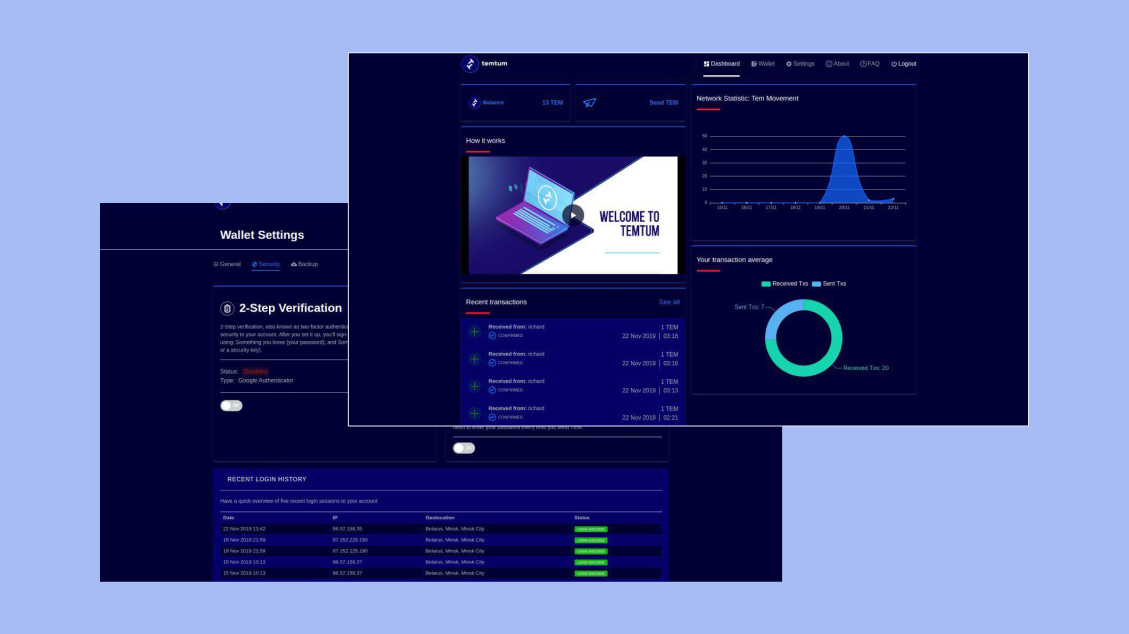
When the customer contacted EffectiveSoft, they only had an idea of a new cryptocurrency in mind. Our team brought the idea to life by developing the Temporal Blockchain platform which became the foundation of the new cryptocurrency together with Temtum API, an application allowing end users to perform transactions (e.g. for crypto asset exchange), and Temtum Wallet, an application helping to transfer the Temtum cryptocurrency (TEM).

The mobile app versions of the Temtum Wallet are available for iOS and Android devices and ensure fast access to the user’s account from any place. The mobile crypto wallet can be backed up to keep the cryptocurrency safe. Even if the application is deleted, the user’s TEMs will be preserved and can be restored.
The near-instant transaction throughput speeds. Thanks to the improved network routing, the removal of the block size limit, and a system architecture, which randomly selects the lead node, the customer managed to reach the simulated transaction throughput speed of 120,000 transactions per second in a laboratory environment.
Lower resource consumption. With the solution, there is no need to verify the block or produce a proof of work, which saves both energy and computing power.
Decentralized scalability. The Blockchain data storage is distributed across a range of specialized nodes, so even low-powered devices can participate in the Temtum network, as there is an option not to store all the data but the latest modifications necessary for successful operation.
Improved security. Cryptographic security is ensured by the quantum-resistant encryption algorithms based on elliptic curves. The security of the user account is enhanced with two-factor authentication, a payment password for every transfer, and login history to track all the login attempts to the personal account.
Our team would love to hear from you.
Fill out the form, and we’ve got you covered.
What happens next?
San Diego, California
4445 Eastgate Mall, Suite 200
92121, 1-800-288-9659
San Francisco, California
50 California St #1500
94111, 1-800-288-9659
Pittsburgh, Pennsylvania
One Oxford Centre, 500 Grant St Suite 2900
15219, 1-800-288-9659
Durham, North Carolina
RTP Meridian, 2530 Meridian Pkwy Suite 300
27713, 1-800-288-9659
San Jose, Costa Rica
C. 118B, Trejos Montealegre
10203, 1-800-288-9659